In the ever-changing world of technology and retai...
news-extra-space

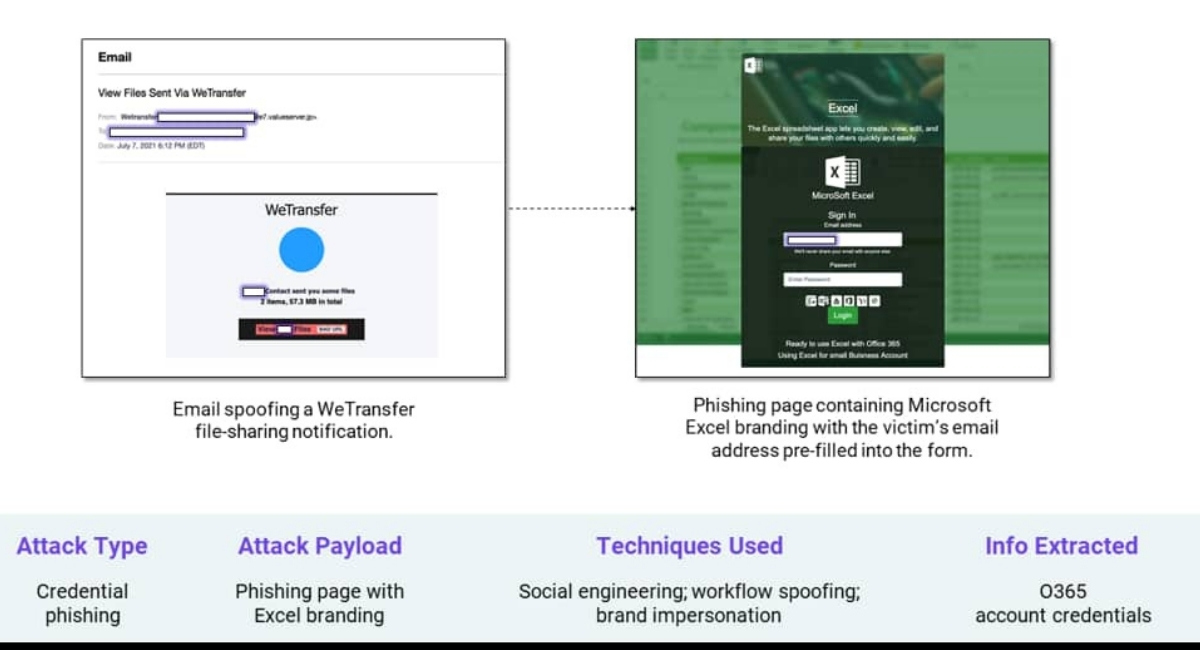 More often, confidential business documents such as contracts, legal documents, and financial records are passed on from one recipient to another via email. And if such fake links to such important documents, it's time to think whether to click them or not. Predicting WeTransfer's popularity, hackers have figured out how to use it to get around security software that detects URLs in emails.
Cybersecurity researchers from Cofense figured out that hackers are now distributing malware called Lampion using fake links. Lampion is a trojan popularly known for stealing sensitive data, such as banking information, passwords, etc. It protrudes known login forms with its own, then sends the submitted data to its command & control servers.
More often, confidential business documents such as contracts, legal documents, and financial records are passed on from one recipient to another via email. And if such fake links to such important documents, it's time to think whether to click them or not. Predicting WeTransfer's popularity, hackers have figured out how to use it to get around security software that detects URLs in emails.
Cybersecurity researchers from Cofense figured out that hackers are now distributing malware called Lampion using fake links. Lampion is a trojan popularly known for stealing sensitive data, such as banking information, passwords, etc. It protrudes known login forms with its own, then sends the submitted data to its command & control servers.
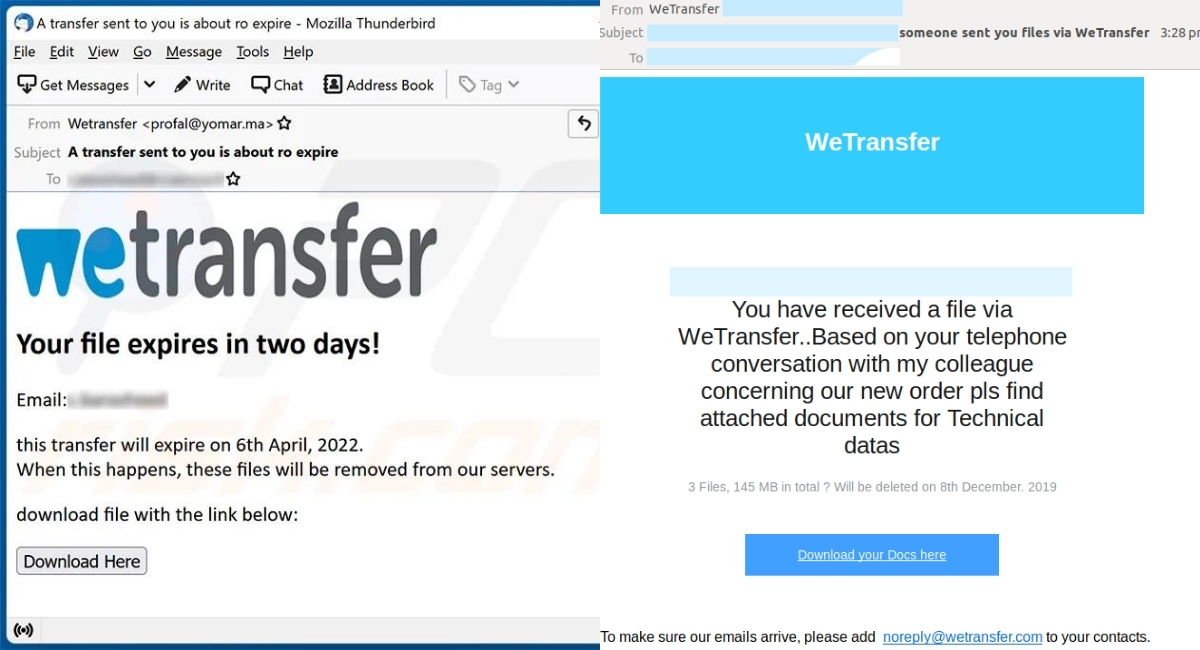 Since 2019, the Lampion trojan has focused mainly on Spanish-speaking targets and using hazarded servers to host its malicious ZIPs.In addition, Lampion was seen abusing cloud services for hosting the malware for the first time, including Google Drive and pCloud, in 2020.
More recently, in March 2022, Cyware claimed an increase in the trojan's circulation, identifying a hostname link to Bazaar and LockBit operations.
However, Cyware also reported that Lampion's authors were actively trying to make their malware harder to analyze by adding more complicated layers and junk code. According to the latest report of Cofense, Lampion is an active and enigmatic threat, and users should be aware of unsolicited emails asking them to download files, even from legitimate cloud services.
Since 2019, the Lampion trojan has focused mainly on Spanish-speaking targets and using hazarded servers to host its malicious ZIPs.In addition, Lampion was seen abusing cloud services for hosting the malware for the first time, including Google Drive and pCloud, in 2020.
More recently, in March 2022, Cyware claimed an increase in the trojan's circulation, identifying a hostname link to Bazaar and LockBit operations.
However, Cyware also reported that Lampion's authors were actively trying to make their malware harder to analyze by adding more complicated layers and junk code. According to the latest report of Cofense, Lampion is an active and enigmatic threat, and users should be aware of unsolicited emails asking them to download files, even from legitimate cloud services.
 When an unknown recipient gets the email, and if they accidentally download the file, they'll receive a ZIP file with a Visual Basic Script (VBS) inside. Also, if run, the script connects to an AWS instance and grabs two DLL files in protected ZIP archives. Afterward, it will automatically activate with no user interaction, and these DLLs are loaded into memory and allow Lampion to operate.
Meanwhile, email is still one of the best ways to distribute viruses, malware, or ransomware, even though email protection tools have improved over the years. In recent times, hackers can take advantage of several free cloud tools, such as calendar organizers, hosting providers, etc., to bypass security measures and distribute malicious code to endpoints worldwide.
When an unknown recipient gets the email, and if they accidentally download the file, they'll receive a ZIP file with a Visual Basic Script (VBS) inside. Also, if run, the script connects to an AWS instance and grabs two DLL files in protected ZIP archives. Afterward, it will automatically activate with no user interaction, and these DLLs are loaded into memory and allow Lampion to operate.
Meanwhile, email is still one of the best ways to distribute viruses, malware, or ransomware, even though email protection tools have improved over the years. In recent times, hackers can take advantage of several free cloud tools, such as calendar organizers, hosting providers, etc., to bypass security measures and distribute malicious code to endpoints worldwide.
Leave a Reply






