In the ever-changing world of technology and retai...
news-extra-space
 He wrote, "Cloudflare Email Routing was in closed beta back when I discovered this vulnerability, with only a few domains having been granted access," Pedersen wrote. "Sadly, I was not invited to the party, so I would have to crash it instead." Pedersen mentions in his blog that it was not difficult to find email lists on Cloudflare, and if a bad guy could get to know this, they would easily exploit the flaw. However, once he discovered the bug, Pedersen could manage to reproduce it multiple times with various personal domains and informed Cloudflare's bug bounty program.
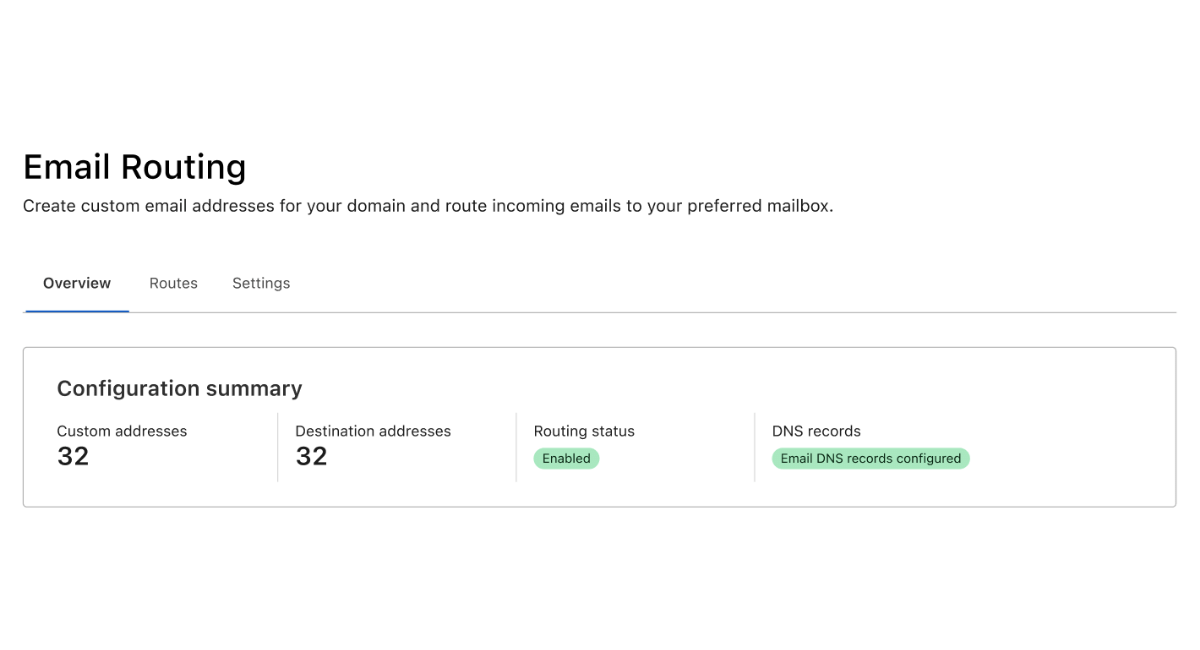
Pedersen mentions in his blog that a hacker could have used the bug to reset passwords that would have threatened other accounts that linked to the hacked account. Cloudflare is a company dealing with content distribution and provides security to websites. In September 2021, they announced the Email Routing Service preliminarily available as a private beta program. This service enables the customers to manage the email address for their respective domains and can redirect emails to the addresses specifically.
He wrote, "Cloudflare Email Routing was in closed beta back when I discovered this vulnerability, with only a few domains having been granted access," Pedersen wrote. "Sadly, I was not invited to the party, so I would have to crash it instead." Pedersen mentions in his blog that it was not difficult to find email lists on Cloudflare, and if a bad guy could get to know this, they would easily exploit the flaw. However, once he discovered the bug, Pedersen could manage to reproduce it multiple times with various personal domains and informed Cloudflare's bug bounty program.
Pedersen mentions in his blog that a hacker could have used the bug to reset passwords that would have threatened other accounts that linked to the hacked account. Cloudflare is a company dealing with content distribution and provides security to websites. In September 2021, they announced the Email Routing Service preliminarily available as a private beta program. This service enables the customers to manage the email address for their respective domains and can redirect emails to the addresses specifically.
 The company's representative stated that they fixed the flaw as soon as they heard about it, "As summarized in the researcher's blog, this vulnerability was disclosed through our bug bounty program. We then resolved the issue and verified that the vulnerability had not been exploited."
Pedersen also writes, "Not only is this a huge privacy issue, but due to the fact that password reset links are often sent to the email address of the user, a bad actor could also potentially gain control of any accounts linked to that email address. This is a good example of why you should be using 2-factor authentication," It is always better to be safe than sorry, so always make a conscious effort to have a 2-step verification to save yourself from cyber hacking.
The company's representative stated that they fixed the flaw as soon as they heard about it, "As summarized in the researcher's blog, this vulnerability was disclosed through our bug bounty program. We then resolved the issue and verified that the vulnerability had not been exploited."
Pedersen also writes, "Not only is this a huge privacy issue, but due to the fact that password reset links are often sent to the email address of the user, a bad actor could also potentially gain control of any accounts linked to that email address. This is a good example of why you should be using 2-factor authentication," It is always better to be safe than sorry, so always make a conscious effort to have a 2-step verification to save yourself from cyber hacking.
Leave a Reply






