(Image credit- ABC News) With the development o...
news-extra-space

US: North Korean Hackers Targeting Health Providers With 'Maui' Ransomware (Image credit- PC Mag)
According to reports, North Korean hackers are currently targeting Mac users with a new malware outbreak known as RustBucket. RustBucket is a stage-one virus that was first identified by cybersecurity company Jamf. It downloads further payloads from a command and control server that is under the control of hackers. The infection is spread using the fake PDF viewer program "Internal PDF Viewer.app." After downloading, RustBucket retrieves the third-stage payload, a signed trojan, followed by the second-stage payload, a signed application posing as an official Apple package identity. What can the RustBucker do? An infected Mac can get its system information collected by RustBucket. Advanced persistent threat (APT) groups will start to attack macOS as it gains market penetration, according to a warning from Jamf. Users of Mac computers should take caution while checking their inboxes, refrain from opening any attachments found in emails from senders they are unsure of, and think about adopting Mac antivirus software. [caption id="" align="aligncenter" width="728"]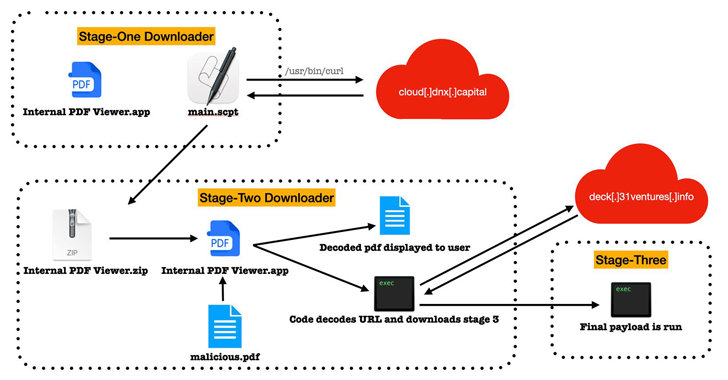 Image credit- The Hacker News[/caption]
Who is responsible for this new malware strain?
According to the reports, BlueNoroff, a Lazarus cluster subgroup from North Korea, is likely to have developed the RustBucket virus.
For the attack to be successful, Gatekeeper defenses must be manually overridden by the victim. BlueNoroff is known for conducting sophisticated cyber-enabled heists against Bitcoin exchanges and the SWIFT system.
In recent months, it has also altered its attack methodology, using job-related lures to trick email recipients into entering their credentials on phony landing pages.
Another illustration of how threat actors are adapting their toolkits to deal with cross-platform malware written in programming languages like Go and Rust is Jamf's discovery of macOS malware.
A cascading supply chain attack that weaponized trojanized installers of the lawful program X_TRADER is also linked to The Lazarus Group, an umbrella term for a group of state-sponsored and criminal hacking groups.
Another well-known threat actor is Kimsuky, which Google's Threat Analysis Group (TAG) is monitoring under the name ARCHIPELAGO.
[caption id="" align="aligncenter" width="820"]
Image credit- The Hacker News[/caption]
Who is responsible for this new malware strain?
According to the reports, BlueNoroff, a Lazarus cluster subgroup from North Korea, is likely to have developed the RustBucket virus.
For the attack to be successful, Gatekeeper defenses must be manually overridden by the victim. BlueNoroff is known for conducting sophisticated cyber-enabled heists against Bitcoin exchanges and the SWIFT system.
In recent months, it has also altered its attack methodology, using job-related lures to trick email recipients into entering their credentials on phony landing pages.
Another illustration of how threat actors are adapting their toolkits to deal with cross-platform malware written in programming languages like Go and Rust is Jamf's discovery of macOS malware.
A cascading supply chain attack that weaponized trojanized installers of the lawful program X_TRADER is also linked to The Lazarus Group, an umbrella term for a group of state-sponsored and criminal hacking groups.
Another well-known threat actor is Kimsuky, which Google's Threat Analysis Group (TAG) is monitoring under the name ARCHIPELAGO.
[caption id="" align="aligncenter" width="820"] Image credit- Tech Times[/caption]
Since 2012, ARCHIPELAGO has been in operation. It is intended for those who are knowledgeable in North Korean policy matters like sanctions, human rights, and non-proliferation.
We previously reported that Google had put in place a number of precautions to combat ARCHIPELAGO, including adding recently discovered hazardous websites and domains to Safe Browsing, which sends notifications to specific people, among other steps.
The phishing tactics used by ARCHIPELAGO have evolved over time, much like those of many other hostile actors. For many years, they sent regular phishing emails posing as Google Account security alerts.
Also read: North Korean hackers lured S. Korean victims with fake Itaewon documents containing malware
How to Protect Yourself as a Mac User
Mac users must now take the same precautions as Windows users to prevent malware infections and the theft of their personal and financial information by hackers.
All software should be kept up to date, each account should have a strong password, and unusual emails and attachments should be ignored, advise cybersecurity experts.
Image credit- Tech Times[/caption]
Since 2012, ARCHIPELAGO has been in operation. It is intended for those who are knowledgeable in North Korean policy matters like sanctions, human rights, and non-proliferation.
We previously reported that Google had put in place a number of precautions to combat ARCHIPELAGO, including adding recently discovered hazardous websites and domains to Safe Browsing, which sends notifications to specific people, among other steps.
The phishing tactics used by ARCHIPELAGO have evolved over time, much like those of many other hostile actors. For many years, they sent regular phishing emails posing as Google Account security alerts.
Also read: North Korean hackers lured S. Korean victims with fake Itaewon documents containing malware
How to Protect Yourself as a Mac User
Mac users must now take the same precautions as Windows users to prevent malware infections and the theft of their personal and financial information by hackers.
All software should be kept up to date, each account should have a strong password, and unusual emails and attachments should be ignored, advise cybersecurity experts.
Leave a Reply






